There is a new wave of malware-infected Android apps that were recently present on the Google Play Store, the official app and content store. Up for grabs are a total of 16 apps with over 20 million installs between them. Delete them now!
So, in case you have any of these Android apps installed on your smartphone, it is best to remove it as soon as possible. Their presence compromises users’ smartphones and the security of their data.
Remove These 16 Android Apps From The Google Play Store
- high speed camera: More than 10 million downloads
- Smart Task Manager: More than 5 million downloads
- Flashlight+: More than 1 million downloads
- Notes calendar: More than 1 million downloads
- K-Dictionary: More than 1 million downloads
- BusanBus: More than 1 million downloads
- flashlight+: More than 500K downloads
- quick note: More than 500K downloads
- Currency converter: More than 500K downloads
- Joycode: More than 100K downloads
- ezTip: More than 100K downloads
- Instagram Profile Downloader: More than 100K downloads
- Notes Ez: More than 100K downloads
- Flash Lite: More than 1K downloads
- calculate: more than 100 downloads
- Flashlight+: 100+ downloads
More than 20 million users may have been affected by the malware

According to a recent to study, more than 20 million Android smartphones and mobile devices may have been affected by malware masquerading as a common utility app. At stake are flashlight apps, currency converters, dictionaries, apps to download information from Instagram, calculators, etc.
Security researchers claim that this malware runs various advertisements in the background to generate money for criminals. In addition, the smartphone will be slower and the battery will consume more, with less autonomy.
The worst of all? With over 20 million confirmed downloads, the scale of the threat is particularly serious. So, if you have any of the apps listed above, remove it as Android/Clicker malware has been detected inside it.
The apps were present in the Google Play Store for Android
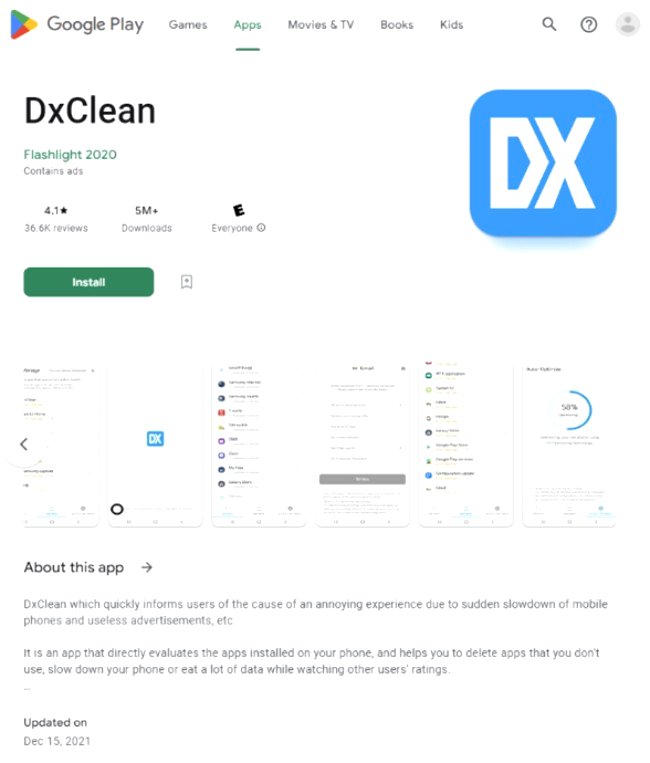
Hidden in general-purpose applications, the malware managed to escape the filters of the Google Play Store. In addition, its way of working was particularly subtle and, after opening, the application started its insidious activity.
In practice, after the first open, it would download its remote configuration using an HTTP request. Once the initial setup was downloaded, the app registered as FCM (Firebase Cloud Messaging) to receive messages Push from the remote server.
Slow and hot smartphone and battery life among symptoms
The app could then start displaying advertisements, without the smartphone user realizing it. The purpose? Generate revenue by displaying advertisements to malware perpetrators.
in the case of a clicker, this malware allows you to perform various actions on the infected smartphone without the user noticing. So, if you have any of these apps, please remove it urgently.
In short, we must be careful with the apps that we install, take into account their reviews and also see what other users say in the Google Play Store reviews.
